Software House Unified Threat Management
Unified Threat
Management
In the face of increasing cybercrime, UTM for a reliable solution that provides comprehensive protection for corporate networks. It enables businesses to more effectively secure their assets against a wide range of threats, minimising the risk of data leakage and business disruption.
Protect your business from cyber attacks with a comprehensive UTM solution from Nicesoft.
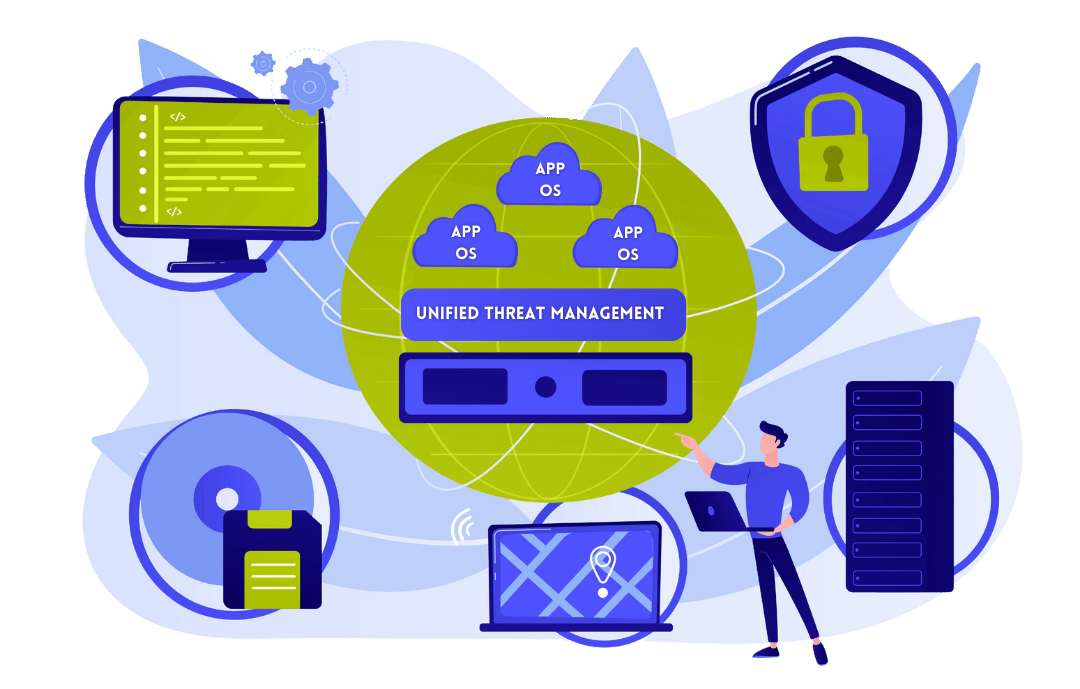
What is UTM system?
UTM (Unified Threat Management) is a comprehensive network security solution that integrates various protective functions into a single device or software. UTM is designed to protect computer networks against a wide range of threats, such as viruses, malware, DDoS attacks, phishing or unauthorised access.

Types of Unified Threat Management
Hardware UTM
These are physical devices that are installed in the corporate network. They act as a gateway between the internal network and the outside world, filtering network traffic and applying various protection mechanisms. Hardware UTMs are typically more powerful and reliable, making them ideal for large companies.
Software UTM
This is software installed on servers or computers that performs similar functions to hardware-based UTMs. They are more flexible as they can be installed on existing infrastructure, allowing for easy upgrades and customisation to meet the specific needs of the company. Software-based UTMs are often the choice of small and medium-sized businesses.
How it works UTM?
The UTM system works by integration of multiple security functions in a single system, which monitors, analyses and protects network traffic in real time.
Stage I - Control of network traffic
The UTM monitors all data entering and leaving the network, acting as a gateway between the internal network and the outside world. In this way, it manages access to network resources in accordance with established rules.
Stage II - Filtering of content and applications
UTM analyses network traffic and blocks access to inappropriate websites, applications and unwanted content, preventing breaches of company policy.
Stage III - Protection against risks
UTM detects and blocks a variety of threats, such as viruses, malware, DDoS attacks or phishing attempts, before they can cause damage. It uses antivirus, intrusion detection and prevention systems (IDS/IPS) and other security tools to do this.
Stage IV - VPN (Virtual Private Network)
UTM enables the creation of secure, encrypted VPN connections, ensuring the confidentiality and integrity of data transferred between remote users and the organisation's network.
Stage V - Management and reporting
UTM offers central management of all security functions, enabling administrators to monitor network activity, generate reports and adjust security policies as required.
Basic functions Unified Threat Management
Firewall
Blocks unauthorised access to the network, manages and controls network traffic according to established policies.
Antivirus / Antimalware
It scans network traffic and files, detecting and eliminating viruses, trojans, worms and other forms of malware.
Content filtering
Blocks access to inappropriate websites and content, preventing breaches of company policy.
VPN (Virtual Private Network)
It provides secure, encrypted remote access to the corporate network, protecting data transferred between employees and the head office.
Intrusion Detection and Prevention System (IDS/IPS)
It monitors the network for suspicious activity and blocks potential threats before they can cause damage.
Protection against spam and phishing
Filters unwanted emails and blocks phishing attempts for confidential information.
Bandwidth and QoS (Quality of Service) management
Prioritises network traffic to ensure adequate bandwidth for critical applications.
Reporting and monitoring
The UTM generates reports on network activity, allowing administrators to monitor security status and take appropriate action.
The role of UTM in network protection
Multiple functions
UTM appliances are hardware-based solutions and offer a wide range of advanced features. They can balance the network load, counteract data leaks, fight viruses, act as an anti-spam gateway, intrusion detection, device reporting, as well as secure email, filter url addresses, packet content, protect the wireless network and much more.
Balancing between NGFW firewall and UTM
Both next-generation firewall (NGFW) and UTM appliances play a key role in ensuring network security. The choice between the two depends on individual needs and preferences, but both solutions allow networks to be effectively protected against a variety of cyber threats.
Advanced protection technologies
The ultimate appliance that enables network protection through proven technologies such as advanced threat protection (ATP), IPS, VPN, mail and web filtering. It is a consolidated solution that combines hardware and software, offering flexibility and adequate bandwidth.
Full control of the application
The device provides full application blocking and admission control, prioritisation and deep 7-layer packet inspection (next-generation firewall). The administrator also receives information about unclassified applications.
Intuitive management
Managing users and system functionalities is easy with an intuitive interface. Solutions can be built on the basis of reports or real-time data, speeding up the response to potential threats.
Merging company branches
With its VPN and WI-FI functions, the device enables secure remote access to company branches. This solution does not require specialised technical skills on the branch side.

Where can UTM be used?
Unified Threat Management can be used in different contexts and environments, where there is a need for comprehensive network protection against cyber threats.
Companies and corporations
UTM is ideal for securing corporate networks, protecting against malware, hacking attacks and other threats. It can also manage access to network resources and filter internet content.
Small and medium-sized enterprises (SMBs)
UTM offers a scalable and integrated solution that is easy to manage and tailored to the needs of smaller organisations that do not have an extensive IT department.
Educational institutions
Schools and universities can use UTM to protect networks from threats, filter content available to pupils and students and monitor online activity.
Financial institutions
Banks and other financial institutions require the highest level of security. UTM can secure transactions, protect customer data and prevent attacks on the IT infrastructure.
Health sector
Hospitals and clinics can use UTM to protect confidential patient data and ensure compliance with information security regulations such as HIPAA.
Government institutions
Government agencies use UTM to protect sensitive information and ensure the security of sensitive data, while managing network access.
Internet service providers (ISPs)
ISPs can use UTM to protect their networks from external and internal threats, as well as to manage bandwidth and quality of service (QoS) for their customers.
Check out our other services
Frequently asked questions
(FAQ)
Here you will find answers to many questions about the UTM system.
UTM (Unified Threat Management) is a comprehensive network security solution that combines various protection functions, such as firewall, antivirus, intrusion detection and prevention system (IDS/IPS), content filtering and VPN, in a single appliance or software.
UTM offers central management of multiple security functions, which simplifies network management and monitoring. With an integrated approach, UTM enhances network protection against a wide range of threats and facilitates compliance requirements.
UTM comes in two forms: hardware (physical device installed on the network) and software (software running on servers or computers). The choice depends on the size of the company, security needs and IT infrastructure.
UTM protects the network from a variety of threats, including viruses, malware, DDoS attacks, phishing, unauthorised access, as well as blocking inappropriate web content and spam.
Yes, UTM is scalable and can be adapted to the needs of small and medium-sized businesses. It provides comprehensive protection, even if the company does not have an extensive IT department.
UTM can be deployed as a physical device on the network or as software on existing servers. It integrates easily into existing infrastructure and can be managed from one central interface.
Modern UTM appliances are designed to minimise the impact on network performance. Through advanced optimisation, they can effectively filter and protect network traffic while maintaining high performance.
UTM is used in a variety of industries, including corporations, small and medium-sized enterprises, educational institutions, financial institutions, healthcare institutions, as well as by government institutions and ISPs.
Yes, regular updates are key for a UTM to effectively protect against new threats. Most UTM solutions offer automatic updates to the threat database and software.
Costs depend on the solution chosen (hardware or software), the range of functions, the number of users and the specific needs of the company. However, it is worth investing in UTM to ensure comprehensive network and data protection.
UTM offers a central management interface that allows you to monitor your network, configure security policies, analyse reports and customise settings as required. Most UTM solutions are intuitive and offer technical support.
Yes, the UTM can protect remote workers with a VPN function that provides secure access to the corporate network from any location, while protecting data transferred between users and the head office.
Newsletter
Sign up for our newsletter to receive the latest content posts directly to your inbox.